An open DNS resolver is a DNS server that responds to recursive DNS queries from any IP address on the internet. Open DNS resolvers are abused for conducting DDoS reflection/amplification attacks against third parties on a daily basis.
To overcome this problem, this article presents how to disable open DNS resolvers on Windows (and only allow resolving for specific IPs), by following the actions below.
- Disable the DNS Recursion on your server
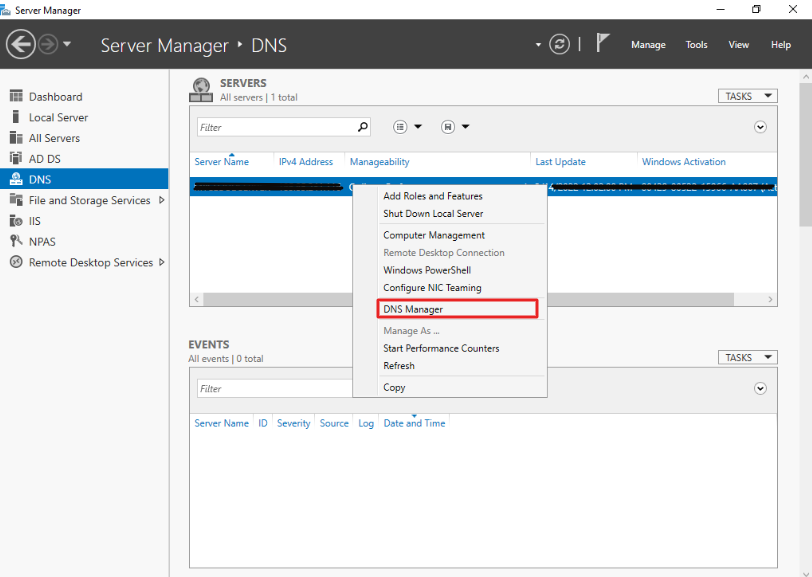
- Log in to your server and open the “DNS Manager”.
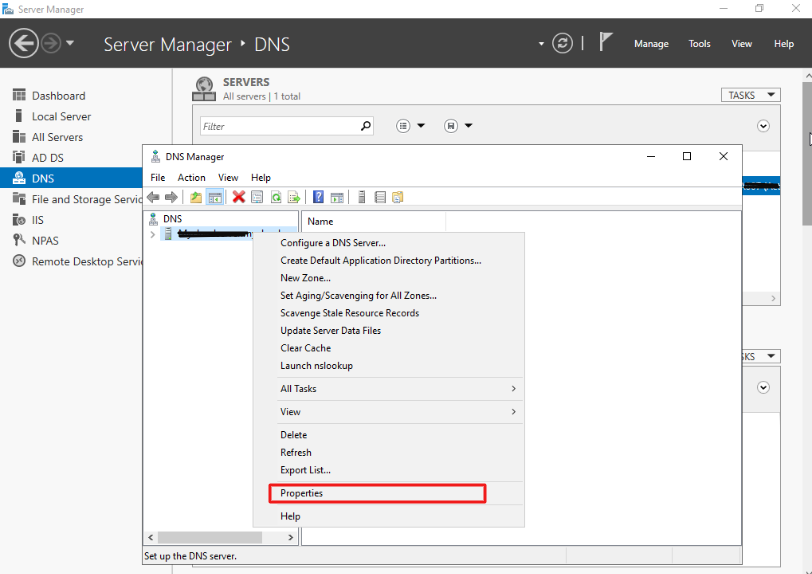
- Right-click on the preferred DNS server and select “Properties”.
- Select the “Advanced” tab and check the “Disable recursion” box in “Server options”.
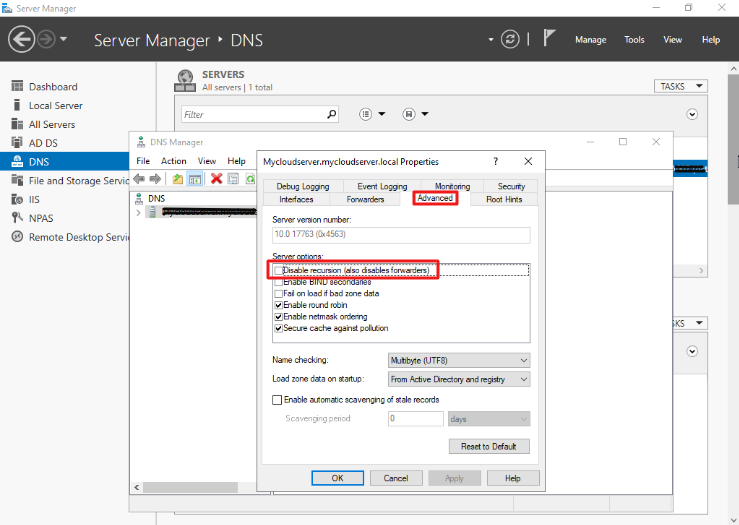
- Click “Apply” and “OK”.
- Block external DNS requests using a built-in Windows Firewall.
Because Windows DNS does not allow you to limit the addresses to which recursive DNS requests are answered, Microsoft recommends this solution.
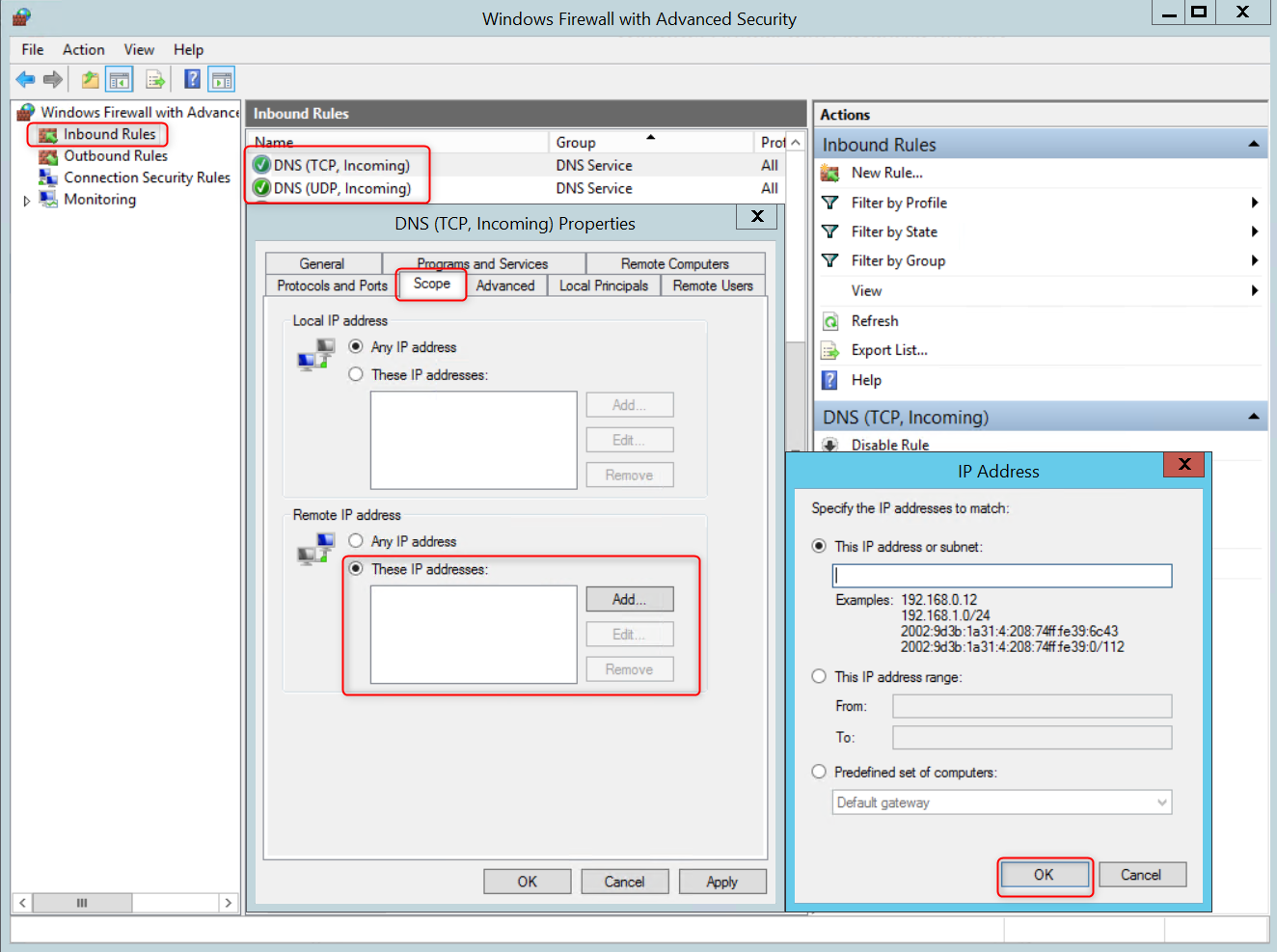
- Log in to your server and open the Windows Firewall with Advanced Security.
- Select the “Inbound Rules”.
- Select the “DNS rules (TCP and UDP)”, and add the following IP addresses in the “Remote IP address” column:
- 127.0.0.1
- Any public IP address assigned to your server.
- Any internal IP address assigned to your server (if you are using an internal network).